In the simplest terms, cloud computing means storing and accessing data and programs over the Internet instead of your computer's hard drive.
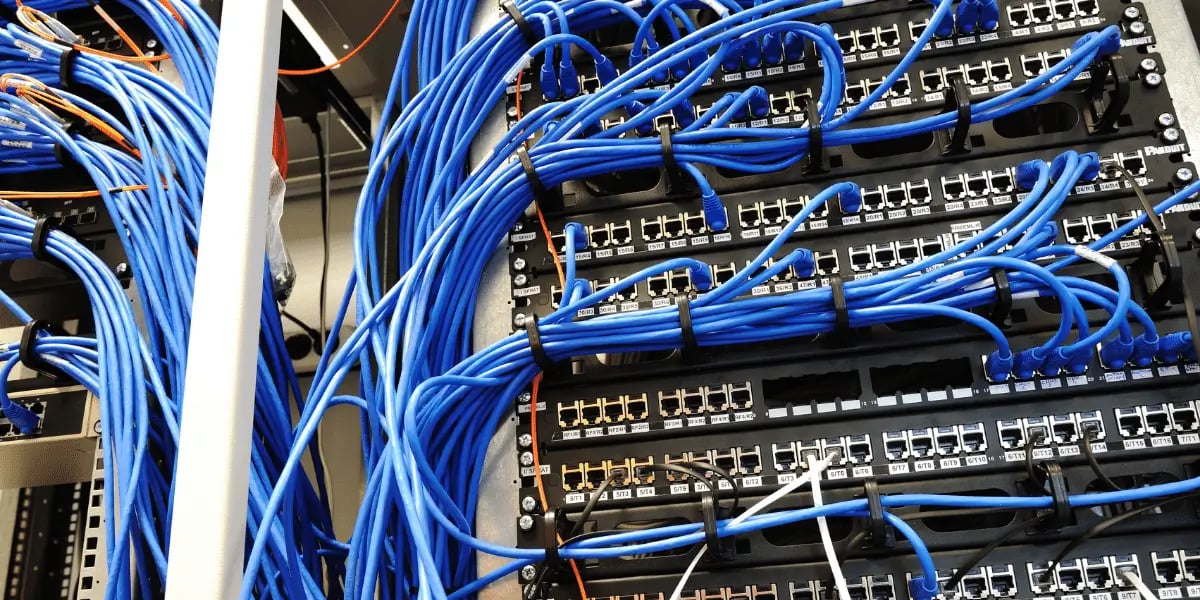
Cloud servers are located in data centers all over the world. By using cloud computing, users and companies do not have to manage physical servers themselves or run software applications on their own machines.
Check out our blog Everything You Need to Know About Cloud Services to learn more!
Having a managed IT service allows your company to stay up to date in many different areas that require constant attention. Services such as alerts, security, patch management, email security, data backup and recovery for many different devices.
These IT services can be provided remotely (while working from home) or in-house. Devices that require managed services such as desktops, notebooks, storage systems, networks, and printers.
Check out our blog Why You Should Be Outsourcing IT with a Managed Service Provider to learn more!
Having a tech support service can make a huge difference in the productivity of your business. Most people don't realize how many areas tech support can actually help in.
Sometimes little problems that occur during the day can turn into bigger problems like misplaced files, email errors, and so much more that can cost you time and money.
The term "Internet of Things" (IoT) refers to the network of physical items or "things" equipped with sensors, software, and other technologies for the meant to connect and exchange data through the internet. These gadgets range from basic household items like Alexa and smart lightbulbs to complex industrial tools.
Check out our blog "The Internet of Things and Remote IT" to learn more!
Vendor management is an essential process for managing the outsourcing of IT work. It allows organizations to control costs, strengthen services and reduce risk throughout this time by implementing technologies that support business needs.
Check out our blog "What You Need to Know About IT Vendor Management" to learn more!
HL7 interface is a frequently used phrase in the healthcare IT marketplace. There are two key parts to defining an HL7 interface.
First, HL7 is "Health Level 7". It's an organization of volunteers who define the data specifications for various message types. These HL7 specification documents provide the framework in which to communicate patient information between healthcare organizations.
Second, "interface" is a communication between systems or applications. Healthcare application vendors need to provide a means within their application for this interaction to take place.
Healthcare vendors will use the HL7 interface specifications for the various message types as a starting point and also will expose an input and/or output interface for their application.
Learn more about HL7 Interfaces in our blog Everything You Need to Know About HL7 Interfaces!
A network assessment is a thorough report and analysis of your company’s current IT framework, security, management, processes, and performance. The goal of the assessment is to identify opportunities for improvement and get a overall view of the current state of your existing network. This helps you make more informed and strategic business decisions that can directly effect your performance.
Click here to sign up for a free network assessment today!
Industry 4.0 can be classified as the significant transformation in the way we produce goods of all sorts with the development of automated and digitized manufacturing.
To learn more, check out our blog Industry 4.0 and Cybersecurity
Malware is a software that is specifically designed to disrupt, damage, or gain unauthorized access to a computer system.
Although malware cannot damage the physical hardware of systems or network equipment, it can steal, encrypt, or delete your data, alter or hijack core computer functions, and spy on your computer activity without your knowledge or permission.
Check out our blog Everything You Need to Know About Malware to learn more!
VoIP, which stands for Voice over Internet Protocol, is a phone system technology that allows users to dial and receive calls without using a local phone service but instead with an internet connection.
Check out our blog An Introduction to VoIP Phone Systems to learn more!
The most basic difference between iMessage and an SMS text message is that an iMessage is sent using an internet connection and the latter is delivered over a cellular network.
A major important difference though, is that iMessage contains end-to-end encryption which allows for security of your data and SMS does not.
Learn more about the differences between SMS and iMessage in our blog SMS vs iMessage!